The Dark Side of Web Push Notifications
With the ever-increasing demand for online selling, marketers are trying to find new ways to attract customers, and in this race of getting something new, they often land up being trapped in some or other malicious acts. Affiliate marketing has created a space of its own in the digital marketing industry. The prime motive of affiliates is to earn money and have little or no connection with the brand's reputation, making them use illegitimate promotion methods. In this article, we will cover one of the standard affiliate traps using – Web Push Notifications.
The Story Behind Web Push Notifications
The web push notification is the newest on the square regarding user engagement channels. We've had mail since the 1960s, and conventional mobile app push-notifications since 2009, but web push notifications date back approximately five years only.
Chrome introduced web push notifications in early 2015 in its 42nd version. The version included two APIs that permitted websites to push notifications to their users. It even allowed notifications after the user has closed the web page, provided the user has granted permission.
In December 2014, Google brought web push notifications kicking into the world by adding them to their message channel on the Chrome Desktop browser.
Initially, the push notifications depended on Google Cloud Messaging to power its outreach and custom API requests, limiting its effectiveness and adoption by brands.
Opera too joined the race later that year. And by December 2015, the marketing landscape experienced a noticeable drift. Google and Mozilla launched built-in support for web push notifications on Chrome 48 and Firefox 44. And there was no looking back on the growth of push notifications in the world of digital marketing.
What are Web Push Notifications?
Web push notifications are message alerts shown on a user's desktop or other devices when the user allows it. These are notifications that any website user can opt-in to receive. Whenever a user visits a website using a web push notification, they see a pop-up message at the top of the page. The website can only send notifications and ads to the users once they approve it.
Websites use these notifications to connect with users after leaving their site to drive greater user engagement and conversions. These clickable content messages can be sent to users' devices by an online site or a web app.
Compared to more popular communication channels such as e-mail, messaging, etc., web push notifications are more straightforward for users to enable and much harder for them to overlook.
Like push notifications, web push notifications can be displayed on a user's device even when the user isn't active on the website. Commonly referred to as 'Browser Push Notifications,' these are best used to engage users.
Although web push notifications serve as a very effective form of marketing and help grab users' attention quickly. Malicious affiliates find ways to use these for their benefit and deceive advertisers and users. Identifying such malicious web push notifications requires continuous monitoring, and brands now focus on ways to be more vigilant and secure their users from such traps.
Web Push Notifications Architecture
Web Push Architecture
The above picture explains the architecture of web push notifications. Once the user allows the website to send messages, it sends the user information to the application server of push ad networks. The push ad network starts serving all the formats of push-up ads they support with scary and tempting creatives for the advertisers in their network. The users often get tempted to click on these messages with a call to action. Malicious affiliates use this medium to insert the affiliate cookies in the user's browser or system and monetize the sales happening from the user's browser.
Where do these notices show up on desktop and mobile?
Web push notifications are pop-up messages with a call-to-action button that appear on users' browsers irrespective of the device or browser they use. Brands and advertisers use them as a quick communication channel to convey their customers' messages, offers, or other information. These alert messages slide in at the top or bottom right-hand side of the desktop screen, depending upon the operating system being used by a user. Web push notifications do not require the user to be on the website to show up, and these are even displayed on the user's browser after leaving the website.
Marketers mainly use these notifications to increase website engagement and encourage visitors to keep coming back to their website, increasing conversions.
Web Push Notification on Desktop
All browsers support web push notifications on the desktop. All the operating systems on the desktop support push notifications, including Safari, Edge, Chrome, and Firefox. The notification opt-in experience varies as per the operating system. For instance -
-
On OS X - Web push notifications are delivered to the notification tab on the top right of the user screen.
-
On Windows & Linux - These notifications are displayed at the foot right of the page.
Here is a table showing the list of all browsers that support web push notifications.
Web Push Notification Mobile Devices
Android is the only mobile operating system supporting web push notifications, and these appear in the notification bar on a mobile device. Mobile push notifications enjoy a high click-through rate, and operating systems like Chrome focus on continuously updating opt-out experiences easier for the users.
Apple is yet to support push notifications on iOS.
Web Push Notification Opt-In Process
Web push notifications are a popular and widely used method of promotion across industries. The ad networks have to seek the user's approval for showing notifications. When the users visit the website using web push notifications, they are prompted for a notification subscription with a default browser prompt. The browser generates a unique registration key for every user who subscribes to notifications.
The affiliates take advantage of users opting in for notifications. They start sending promotional messages that do not exist, redirect users to advertisers' websites, earn money through PPC promotions, or inject affiliate cookies to monetize sales happening from users' browsers, and the list is never-ending.
How do affiliates use Web Push Notifications?
Affiliates are rewarded for getting legitimate users and driving more sales for brands they choose to promote. But the threat actors use different ways to maliciously promote the brands and earn commissions without driving actual sales or attracting legitimate users.
Affiliates use different promotional methods to attract users for the advertisers in their network. Web push notification is one of the methods that easily allows them to display fake advertisements and inject affiliate cookies in the user browser. The malicious acts end up with brands losing their reputation and marketing budgets.
The affiliates use mediums like their social media platforms, websites, and more to promote the advertiser's products and services. Affiliates use various promotional platforms to direct users to their websites. They then add web push notifications on their website, already driving user traffic. Once users allow them to send messages by opt-in process, they start sending advertisements in push notifications.
These advertisements are lucrative and attractive and tend to grasp user attention. When the user clicks on any push notification, the affiliates inject their affiliate cookie and then earn a commission from advertisers for getting more users or driving sales.
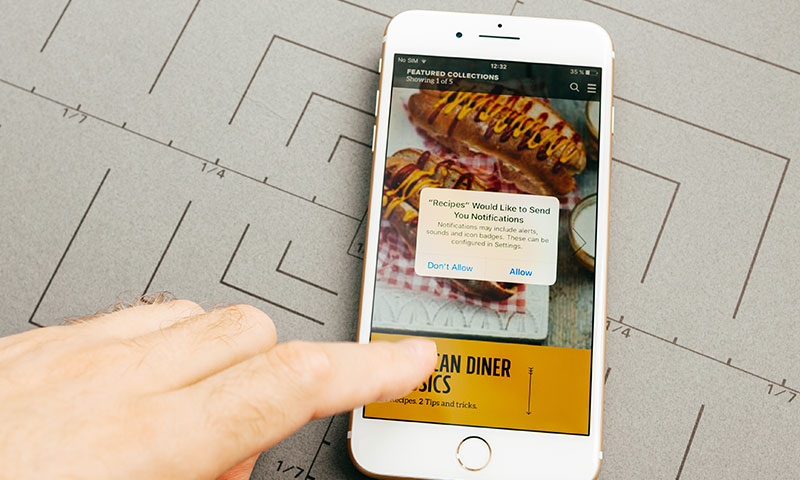
Affiliates can use web push notifications to scam users in multiple ways. It is important to remember that browser notifications need users to consent to their use. The websites display a small text box below the address bar on a webpage, and the box asks if the website in question can send notifications. That website can send notifications outside the browser via the operating system messaging broadcast system if the user agrees.
Malicious marketers often take advantage of this feature. For example, the message box shows permission to play a video on a streaming website instead of asking for the user's consent. If the user clicks, the user gets redirected to another website to watch the video. Now, affiliates can use this to redirect the users to the advertiser's page and earn commission via a pay-per-click model, inject affiliate cookies to monetize the sales, collect user information to be sold on the dark web, and the list continues.
Also, for every website, the user clicks on 'allow.' the user grants permission to the malicious affiliate to send notifications and open the way for abuse.
The image shows an example of a deceptive alert message that forces the user to allow notifications.
Here are a few use cases of how affiliates can use web push notifications to deceive users and advertisers.
Use Case 1 – Web Push Notification activated on Publisher Website
A user wants to buy clothes online and visits an affiliate website VPTshop.com. As the user is on the website, he receives a pop-up seeking permission to display push notifications & the affiliates register a service worker (a script that will be executed when a push notification is received).
The user then clicks on the 'Allow' button displayed on the user browser and grants permission to the affiliates to show notifications. The affiliates start displaying malicious browser notifications in the user browser. These notifications show lucrative advertisements for Guiseme.com with a discount coupon on purchases from Guieseme.com.
The user is attracted to the discount on his purchase and clicks on the push notification. He gets redirected to the advertiser website Guiseme.com, and no deal shows up. The coupon is fake and doesn't deliver as shown in the web push notification. But the affiliate cookie gets injected into the user system, and the affiliates monetize all sales from the user browser.
The advertiser here loses the brand reputation because users get scammed with fake coupons, the user experience gets impacted, and brands end up paying malicious affiliates.
Use Case 2 – Web Push Notification activated on Publisher Website.
A user looking to buy clothes online discovers a web extension offering discounts on one of the brands, Guiseme. The user then installs the extension to avail discounts on his purchases, and Adware gets installed in the user system bundled up with this extension. The malicious affiliates have used this extension to inject Adware into the user's system. Once the Adware gets installed, it can infect the user system in multiple ways, bombarding the user system with push ad notifications. The malicious Adware can infect a user's system by continuously displaying push ads of the advertisers in the affiliate network.
When the user clicks on any of these notifications, the affiliate can inject the affiliate cookie and steal their personal information or monetize the sales from the user's system. The push notifications can also redirect the users to the advertiser's website. But this way of attracting traffic is not legitimate and gives a poor user experience.
Impact of Malicious Web Push Notifications
Like any malicious affiliate trap, push notifications can damage any brand's image, revenue, and customer experience.
-
Brand Reputation: The malicious affiliates use web push notifications by displaying fake offers and attracting customers to the advertiser's website. It directly hits the brand's reputation, and customers lose their trust. Most users are not aware of the indirect ways of marketing and assume that the brand is pushing these messages.
-
Advertising ROI: The advertisers pay affiliates commissions to get new users and drive incremental sales. The malicious affiliates attract users by means that are not legitimate and consume the brands' marketing budget. Web push notifications are used to redirect a user from one website to an advertiser's website and inject their affiliate cookies to earn a commission.
-
Customer Experience: The customer's experience is hampered as the offers are fake or delusive. The customer journey is hijacked as they get directed to the advertiser's website upon clicking on any web push notification.
How to defend from malicious affiliates?
Virus Positive Technologies (VPT) is pioneering the market of Affiliate Fraud Management & Brand Protection. VPT's disruptive methodology identifies non-compliant behaviors that hurt conversion rates and damage the brand's reputation. A few are listed below:
-
Pop-up ads
-
Brand-bidding (the use of brand name keywords that are prohibited)
-
Incentives (any incentive practices, such as offering cash for clicking)
-
Aggressive & Misleading creatives
-
Malvertising (injecting malicious ads or links into legitimate ads)
-
Unauthorized Creatives (the visuals or links for custom ads)
-
Pre-landers & fake browser alerts
-
Google Display Network (any promotional activity on the GDN platform)
-
Spamming and Bundling
-
Forced redirects (clicks injected into consumer web sessions that divert customers to competitor offerings)
VPT offers a range of Brand Compliance Monitoring tools based on customized customer requirements and Affiliate Management Services to track and monitor the activities of the publishers in the advertiser's affiliate network.
Our digitized services protect your brand reputation and give your customer an undisrupted experience. Visit our website www.viruspositive.com or write to us at sales@viruspositive.com.


.jpg)