Malicious Bots - All You Need To Know
What are Bots?
Bots or internet robots are computer programs one typically interacts with and are meant to make life a little easier. These are automated software designed by human programmers to do web tasks or simulate human activity.
These are utilized to perform repetitive tasks that a human would otherwise have to complete, and Bots are more efficient and faster than humans at such repetitive tasks.
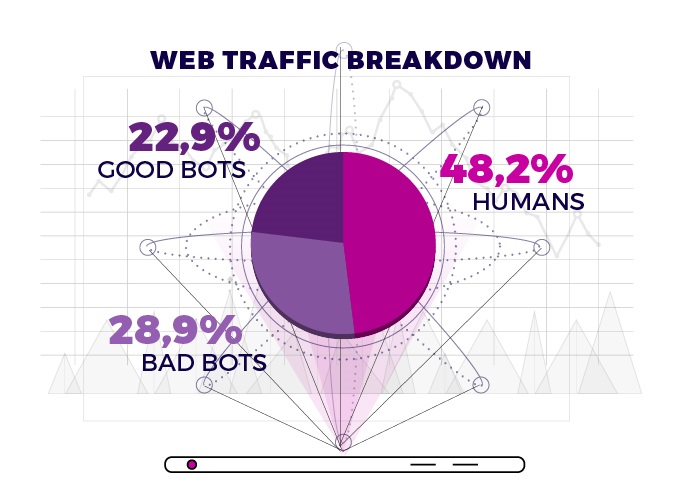
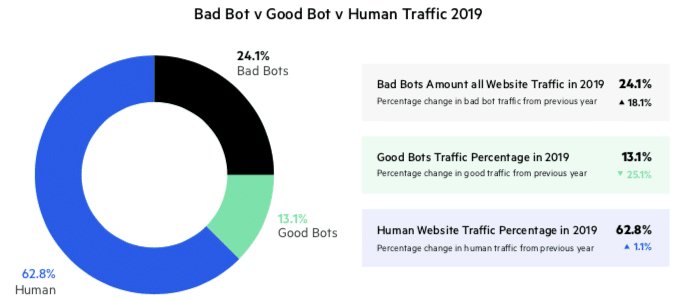
In a world where more than 50% of the internet traffic comes from bots, the scope of fraud and malicious acts is higher than ever imagined.
How do bots work?
Bots operate over a network. The bots communicate using internet-based services, such as instant messaging. Bot traffic interacts with web pages, chat with users, scan for content, gathers search trends, and a lot more.
In the world of affiliate marketing, bots are usually connected to ad fraud scandals, security breaches, cybercrime, and other malicious activities.
What are Botnets?
Malware often infects end-user devices, intending to enlist them into a network – this is referred to as BotNet. Any device that becomes infected starts communicating with a Command and Control (C&C) center and can perform automated activities under the attacker's central control. The botnet can provide a path to launch remote-control attacks and gather sensitive information from the users at large.
What are Malicious Bots?
A bot malware can infect your device, gather passwords, collect data, distribute spam, and attach to an infected host system. Bad bots interact with applications in the same way as legitimate users. They allow bot operators, attackers, unsavory competitors, and fraudsters to perform a wide array of malicious activities such as web scraping, data mining, financial data fraud, digital ad fraud, spam, transaction fraud, and more. These malicious bots take up a larger space than good bots on the internet.
Types of Malicious/ Bad Bots
- Impersonators – Bots assume false identities to bypass the security walls. These bots look natural and are used for distributed denial-of-service (DDoS) attacks.
- Web Scrapers – This type of bot is used for unauthorized data extraction. Fraudsters use scraper bots to steal high-quality and keyword-rich content from other websites.
- Spambots – Attackers inject spam links into forums, discussions, and comments sections on social media. They can fetch the personal information of the users through such forms.
- Click Bots – These hit the CPC model of advertising. These bots intentionally visit sites and click on ads to warp ad campaign data and burn through an advertiser's budget.
- Download Bots – These bots automatically download software or mobile apps on the user's devices.
- Transfer Bots – These bots are responsible for forced redirects. The Bots attach themselves to websites, and when a user clicks through, they get redirected to another site set up by a fraudster.
- Credential Stuffing – This is a type of cyber-attack where the data breach obtains the users' login credentials, and this data is used for logging in to another service.
- Hacker Tools are designed to infect sites and steal data from vulnerable websites.
How can companies stop malicious bot activity?
Bot management solutions can differentiate harmful bot activity from user activity via machine learning. These can identify and block malicious bots based on behavioral analysis that detects threats.
Virus Positive Technologies helps companies stop malicious bots without impacting the user experience. To learn more, connect with our team of experts – sales@viruspositive.com.
You can also visit our next blog on Typosquatting.